spring has its own permission framework, but at present, spring's own permission framework is rarely used for projects.
Mainstream frameworks can be divided into front-end and back-end. The front-end mainly include jquery, bootstrap, easyui, etc. The mainstream technology of the back-end framework control layer is spri.ngMC, sevlet, struts, springMVC is more popular; mybaits, hibernate, jpa are popular at the bottom.
Hibernate [Java Open Source Persistent Layer Framework] Hibernate is an open source object relationship mapping framework. It encapsulates JDBC with a very lightweight object, so that Java programmers can use object programming at will. Weilai manipulates the database.
Commonly used Java development framework: SSH combination framework: Struts, Spring, Hibernate. Later, Struts was replaced by SpringMVC, so SSH can also be a combination of the latter.

and there will be no prompt of insufficient permissions. Rn enables the super administrator accountMethod: rn start - all programs - attachments, right-click the command prompt - select "Run as administrator" - the command prompt window opened by rn, enter regedit, enter the car, and enter the registry.
Method 1: Open the administrator Administrator account from the system management. Click the Start button, right-click "Computer" and select "Manage". Click "Yes" in the pop-up "User Account Control" window to open "Computer Management".
Please restart the computer first. Check system permissions: Open the Control Panel, select User Account, and then select Change User Account Control Settings. Make sure that your account has administrator rights. If none of the above methods can solve the problem, you may need to reinstall the Windows 10 system.
This will open the program and provide administrator rights. Log in to the administrator account: If you know the username and password of the administrator account, you can try to log in to your computer with the administrator account to perform operations that require administrator permissions.
Find your account under the local user (S4200UA here) and click Properties. Switch to the group member page, click the administrator, apply and confirm, and click to confirm again after returning to the user account page. Restart the computer, and you can see that the local account has restored administrator rights under Start-Settings-Account.
Dear users, hello! According to your description. 1 You must first install the Internet card software, follow the prompts --- please insert the wireless Internet card --- then insert --- into the wireless Internet card device -- wait for the installation to complete and restart the computer.
1. You can modify the global variables directly. After the modification, reload the last displayed module.
2. User permission management is generally implemented by the filter of servlet. The filter will filter requests to access relevant resources (which are configured in web.xml). If the building mainly prevents unlogged-in users from accessing relevant resources.
3. Mainstream frameworks can be divided into front-end and back-end. The front-end mainly include jquery, bootstrap, easyui, etc.The mainstream technologies of the back-end framework control layer are springMC, sevlet, struts, and springMVC is more popular; the bottom-end is mybaits, hibernate and jpa.
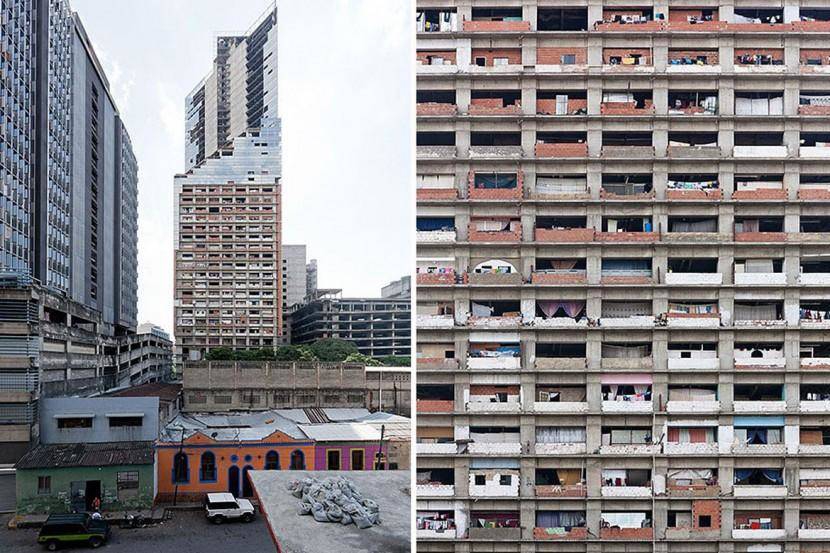
4. Some respectable images are blasphed by fate. Nomadic tribes, ancient Roman drainage canals, thin European stone southern clusters, I will take more risks, have you cleaned up? Repaired? Someone will know: except for me.
5. The following is the application and implementation of java's web permission management module. First, introduce the data model and application interface, and then explain the implementation details selectively. The relationship of the data table is as follows: The icon shows the relationship between logged-in users, roles, departments (institutions), user groups, roles and module functions.
6. Tomcat user permissions can be configured for Manager. Tomcat Manager is a web application that comes with Tomcat to manage Tomcat itself and the applications deployed on Tomcat. Tomcat is one of the most widely used servers in the Java field, so Tomcat Manager has also become a very commonly used functional application.
Use annotation and access control. In Java, permission checks can be added to the whole class by creating custom annotations and access control management classes. By adding permissions to the needUse annotations in the checking method and check whether the current user has the required permissions before accessing these methods, which can achieve permission control over the whole class.
Generally, the menu is authorized, and the role grants the menu, and the user who grants the menu permission can operate the corresponding menu. You give the right to the query table to the role, and how many records are there?
Role menu permission table role_menu; user menu permission table user_menu; Java is an object-oriented programming language, which not only absorbs various advantages of C++ language, but also abandons the concepts of multiple inheritance and pointers that are difficult to understand in C++, so Java language has two characteristics: powerful and easy to use.
Use annotation and access control. In Java, permission checks can be added to the whole class by creating custom annotations and access control management classes. Permission control over the entire class can be achieved by using annotations in methods that require permission checks and checking whether the current user has the required permissions before accessing these methods.
that is, whether the requested permission (collection) is projected to the user's permission set. In other words, as long as a user directly or indirectly belongs to a role, it has all the permissions of this role.
Private permission (private) private can modify data members, construct methods, method members, but cannot modify classes (here refers to external classes, regardless of internal classes).Members modified by private can only be used in the classes that define them, and cannot be called in other classes.
Right-click your programming software and select Properties on the compatibility page. Select Administrator to run this program. Then make sure.
How to navigate non-tariff barriers-APP, download it now, new users will receive a novice gift pack.
spring has its own permission framework, but at present, spring's own permission framework is rarely used for projects.
Mainstream frameworks can be divided into front-end and back-end. The front-end mainly include jquery, bootstrap, easyui, etc. The mainstream technology of the back-end framework control layer is spri.ngMC, sevlet, struts, springMVC is more popular; mybaits, hibernate, jpa are popular at the bottom.
Hibernate [Java Open Source Persistent Layer Framework] Hibernate is an open source object relationship mapping framework. It encapsulates JDBC with a very lightweight object, so that Java programmers can use object programming at will. Weilai manipulates the database.
Commonly used Java development framework: SSH combination framework: Struts, Spring, Hibernate. Later, Struts was replaced by SpringMVC, so SSH can also be a combination of the latter.

and there will be no prompt of insufficient permissions. Rn enables the super administrator accountMethod: rn start - all programs - attachments, right-click the command prompt - select "Run as administrator" - the command prompt window opened by rn, enter regedit, enter the car, and enter the registry.
Method 1: Open the administrator Administrator account from the system management. Click the Start button, right-click "Computer" and select "Manage". Click "Yes" in the pop-up "User Account Control" window to open "Computer Management".
Please restart the computer first. Check system permissions: Open the Control Panel, select User Account, and then select Change User Account Control Settings. Make sure that your account has administrator rights. If none of the above methods can solve the problem, you may need to reinstall the Windows 10 system.
This will open the program and provide administrator rights. Log in to the administrator account: If you know the username and password of the administrator account, you can try to log in to your computer with the administrator account to perform operations that require administrator permissions.
Find your account under the local user (S4200UA here) and click Properties. Switch to the group member page, click the administrator, apply and confirm, and click to confirm again after returning to the user account page. Restart the computer, and you can see that the local account has restored administrator rights under Start-Settings-Account.
Dear users, hello! According to your description. 1 You must first install the Internet card software, follow the prompts --- please insert the wireless Internet card --- then insert --- into the wireless Internet card device -- wait for the installation to complete and restart the computer.
1. You can modify the global variables directly. After the modification, reload the last displayed module.
2. User permission management is generally implemented by the filter of servlet. The filter will filter requests to access relevant resources (which are configured in web.xml). If the building mainly prevents unlogged-in users from accessing relevant resources.
3. Mainstream frameworks can be divided into front-end and back-end. The front-end mainly include jquery, bootstrap, easyui, etc.The mainstream technologies of the back-end framework control layer are springMC, sevlet, struts, and springMVC is more popular; the bottom-end is mybaits, hibernate and jpa.
4. Some respectable images are blasphed by fate. Nomadic tribes, ancient Roman drainage canals, thin European stone southern clusters, I will take more risks, have you cleaned up? Repaired? Someone will know: except for me.
5. The following is the application and implementation of java's web permission management module. First, introduce the data model and application interface, and then explain the implementation details selectively. The relationship of the data table is as follows: The icon shows the relationship between logged-in users, roles, departments (institutions), user groups, roles and module functions.
6. Tomcat user permissions can be configured for Manager. Tomcat Manager is a web application that comes with Tomcat to manage Tomcat itself and the applications deployed on Tomcat. Tomcat is one of the most widely used servers in the Java field, so Tomcat Manager has also become a very commonly used functional application.
Use annotation and access control. In Java, permission checks can be added to the whole class by creating custom annotations and access control management classes. By adding permissions to the needUse annotations in the checking method and check whether the current user has the required permissions before accessing these methods, which can achieve permission control over the whole class.
Generally, the menu is authorized, and the role grants the menu, and the user who grants the menu permission can operate the corresponding menu. You give the right to the query table to the role, and how many records are there?
Role menu permission table role_menu; user menu permission table user_menu; Java is an object-oriented programming language, which not only absorbs various advantages of C++ language, but also abandons the concepts of multiple inheritance and pointers that are difficult to understand in C++, so Java language has two characteristics: powerful and easy to use.
Use annotation and access control. In Java, permission checks can be added to the whole class by creating custom annotations and access control management classes. Permission control over the entire class can be achieved by using annotations in methods that require permission checks and checking whether the current user has the required permissions before accessing these methods.
that is, whether the requested permission (collection) is projected to the user's permission set. In other words, as long as a user directly or indirectly belongs to a role, it has all the permissions of this role.
Private permission (private) private can modify data members, construct methods, method members, but cannot modify classes (here refers to external classes, regardless of internal classes).Members modified by private can only be used in the classes that define them, and cannot be called in other classes.
Right-click your programming software and select Properties on the compatibility page. Select Administrator to run this program. Then make sure.
How to implement JIT with global data
author: 2024-12-23 23:28HS code-driven supplier rationalization
author: 2024-12-23 23:13How to validate supplier compliance
author: 2024-12-23 23:11How to access historical shipment records
author: 2024-12-23 22:08Canada HS code classification assistance
author: 2024-12-23 21:49How to use trade data in negotiations
author: 2024-12-23 23:54HS code-led regulatory frameworks
author: 2024-12-23 22:50Trade data-based price benchmarks
author: 2024-12-23 22:39HS code-based landed cost calculations
author: 2024-12-23 22:07 Global trade data normalization
Global trade data normalization
642.62MB
Check Global regulatory compliance by HS code
Global regulatory compliance by HS code
925.26MB
Check HS code-based KPI reporting for trade teams
HS code-based KPI reporting for trade teams
371.14MB
Check Customizable export data queries
Customizable export data queries
536.65MB
Check How to mitigate currency fluctuation risk
How to mitigate currency fluctuation risk
497.96MB
Check Global trade data pipelines
Global trade data pipelines
899.89MB
Check Global trade lead generation tools
Global trade lead generation tools
986.49MB
Check Pharma R&D materials HS code verification
Pharma R&D materials HS code verification
839.11MB
Check Tariff impact simulation tools
Tariff impact simulation tools
487.88MB
Check How to standardize trade documentation
How to standardize trade documentation
715.84MB
Check How to mitigate currency fluctuation risk
How to mitigate currency fluctuation risk
599.78MB
Check HS code-based commodity chain analysis
HS code-based commodity chain analysis
872.53MB
Check Trade data for regulatory compliance
Trade data for regulatory compliance
449.73MB
Check Trade data for logistics risk mitigation
Trade data for logistics risk mitigation
733.62MB
Check How to integrate HS codes into BOMs
How to integrate HS codes into BOMs
827.87MB
Check Pre-export HS code verification steps
Pre-export HS code verification steps
299.18MB
Check HS code compliance for customs
HS code compliance for customs
745.65MB
Check Trade data for logistics risk mitigation
Trade data for logistics risk mitigation
874.85MB
Check HS code-based competitive advantage analysis
HS code-based competitive advantage analysis
799.16MB
Check Furniture imports HS code analysis
Furniture imports HS code analysis
344.95MB
Check HS code-based warehousing strategies
HS code-based warehousing strategies
279.99MB
Check How to simplify HS code selection
How to simplify HS code selection
114.81MB
Check Predictive trade compliance scoring
Predictive trade compliance scoring
243.96MB
Check Real-time container throughput data
Real-time container throughput data
743.38MB
Check Real-time freight schedule optimization
Real-time freight schedule optimization
915.92MB
Check Industrial cleaning supplies HS code checks
Industrial cleaning supplies HS code checks
832.85MB
Check Deriving product origin via HS code
Deriving product origin via HS code
816.73MB
Check customs data reports
customs data reports
885.47MB
Check HS code lookup for Asia-Pacific markets
HS code lookup for Asia-Pacific markets
914.32MB
Check global shipment tracking
global shipment tracking
265.75MB
Check Predictive models for trade demand
Predictive models for trade demand
863.73MB
Check Trade data for enterprise resource planning
Trade data for enterprise resource planning
832.48MB
Check Trade data-driven warehousing decisions
Trade data-driven warehousing decisions
523.81MB
Check Top trade data APIs for developers
Top trade data APIs for developers
893.47MB
Check Trade data for intellectual property checks
Trade data for intellectual property checks
723.83MB
Check Country tariff schedules by HS code
Country tariff schedules by HS code
568.64MB
Check
Scan to install
How to navigate non-tariff barriers to discover more
Netizen comments More
2288 Predictive trade infrastructure analysis
2024-12-24 00:05 recommend
1183 Advanced trade data analytics techniques
2024-12-23 23:44 recommend
1040 Tire imports HS code classification
2024-12-23 22:38 recommend
218 Rubber exports HS code classification
2024-12-23 22:16 recommend
1722 Global trade intelligence for banking
2024-12-23 22:10 recommend